Full Network Audit
Full network audit at each site
Day(s) onsite (Senior Engineer) Day(s) write up/field follow emails
This would cover:
Written report & recommendations produced
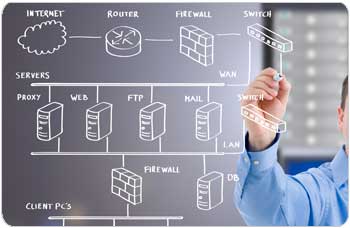
Network audit
Security and backup
Disaster recovery
Vulnerability
Ability to recover/time
Recommendations
Scope –
- External Network Penetration Test
- Servers
- Desktops
- Wifi / Access points
- Firewall rules
- Switches
- Review of Procedures
- Phone systems
- Remote / mobile devices (BYOD)
- Applications review
- Review of Backup/DR/BCP
An enterprise-grade network audit can vastly improve your network’s performance. From BYOD to bandwidth demands...
Limitations of Base level network penetration test
Our rationale for this approach is simple. Consider these two examples:
- An email containing malware is downloaded by a user internally. A perimeter network penetration test wouldn’t identify this vulnerability throughout of date antivirus software and/or domain permissions.
- Another example, a flat network that is open to allow guest access, but does not utilise network separation between guests and office staff. This environment would expose core systems to public view. This would introduce vulnerabilities that would not be uncovered by a public-facing penetration test.
Contact the Precept Security team on 0800 122 3010 or email hello@precept.it to take the next steps to protect your network and critical business data.